Today, organizations are expected to manage private data appropriately and take every precaution to protect it from loss, unauthorized access or theft. We look at what data can be at risk and what can be done to protect it
by John Stringer, Sophos
 Virtually every organization acquires, uses and stores personally identifiable information (PII). Most have it for their employees and, depending on their area of business, may also have it for a wider group including customers, patients, residents and students. Misusing, losing or otherwise compromising this data can carry a steep financial cost and damage an organization’s reputation. There are a number of challenges companies face and steps they can take to protect themselves against data breaches and ensure the safety of this sensitive information.
Virtually every organization acquires, uses and stores personally identifiable information (PII). Most have it for their employees and, depending on their area of business, may also have it for a wider group including customers, patients, residents and students. Misusing, losing or otherwise compromising this data can carry a steep financial cost and damage an organization’s reputation. There are a number of challenges companies face and steps they can take to protect themselves against data breaches and ensure the safety of this sensitive information.
Not so long ago, the most common way people protected their personally identifiable information (PII) was to pay for an unlisted telephone number. Today, there are many types of PII—and it’s not just businesses that use and must protect PII. Schools, universities, healthcare facilities, retailers, government offices and many other organizations also acquire, process and store highly sensitive records.
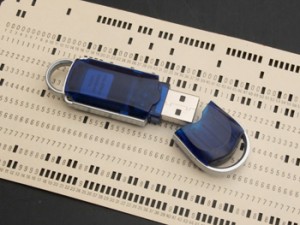
Use of technology has resulted in much greater flexibility and speed when it comes to making purchases, processing payments and managing data records. However, it has also led to a growing data loss prevention (DLP) problem that puts people’s PII at risk.
There are two types of data loss: accidental and malicious. Human error or carelessness as well as a lack of data security processes in an organization can lead to accidental loss, including something as simple as sending an email attachment containing PII to the wrong recipient. Malicious data breaches, on the other hand, are deliberate internal or external attacks on an organization’s data systems.
PII explained
PII, according to the U.S. Office of Management and Budget, is any information that can be used to uniquely identify, contact or locate an individual, or can be used with other sources to uniquely identify a person. It consists of a broad range of information that can identify individuals, including dates of birth, addresses, driver’s license numbers, credit card numbers, bank account numbers, health and insurance records, and much more. Unless your organization keeps no payroll-related data about its employees, it has PII it needs to protect.
While most adults are careful about disclosing their personal information, this issue is particularly sensitive for organizations that have information on minors, such as schools, councils and medical services. It becomes incumbent on the holder of that PII to be vigilant about its use and access. According to the U.S. General Accounting Office, 87% of the U.S. population can be uniquely identified using only gender, date of birth and ZIP code. So it is not just the most obvious types of PII, like credit card numbers, that require protection.
Regardless of how the data is lost, the cost of a data breach can be huge. Fines are one of the most widely-known consequences of losing personal data, and they can be very expensive (e.g., up to $1.5 million per year in the case of a breach of healthcare records in violation of the Health Insurance Portability and Accountability Act [HIPAA] or up to £500,000 from the UK Information Commissioner). However, the consequences extend much further and include reputation damage, loss of customer trust, employee dissatisfaction and attrition, and clean-up costs following the breach.
Organizations must ensure they consider data in all three states when protecting their PII:
- data in use – data on endpoints being used by employees to do their jobs
- data at rest – information stored on endpoints, file servers and information repositories like Exchange servers, Sharepoint and web servers
- data in motion – data sent over networks.
Use policies
 IT managers must balance the desire to tightly control and protect PII with the needs of employees to use the data to perform their jobs. Think of it in terms of CIA: confidentiality, integrity and availability of PII. The goal is to create and enforce AUPs that clearly define which data is most sensitive and which employees are allowed to access and use it in their work. Form a team to help identify and prioritize all the PII your organization possesses. The team typically would include IT operations, the security team and data controllers – who know what data is available and where it is located – and representatives of the HR and legal departments, who have expertise in compliance regulation and legal obligations. This team can help you define your organization’s acceptable use policies for handling and storing PII.
IT managers must balance the desire to tightly control and protect PII with the needs of employees to use the data to perform their jobs. Think of it in terms of CIA: confidentiality, integrity and availability of PII. The goal is to create and enforce AUPs that clearly define which data is most sensitive and which employees are allowed to access and use it in their work. Form a team to help identify and prioritize all the PII your organization possesses. The team typically would include IT operations, the security team and data controllers – who know what data is available and where it is located – and representatives of the HR and legal departments, who have expertise in compliance regulation and legal obligations. This team can help you define your organization’s acceptable use policies for handling and storing PII.
Questions for developing PII acceptable use policies (AUPs):
- Who needs access to PII to do their jobs?
- What regulatory mandates must your organization comply with?
- What are your data security vulnerabilities?
- What data can be transferred within the organization? Sent outside to third parties?
- What rules and permissions for data transfer does your organization have or need?
- Is encryption required before data can be transmitted or stored on portable devices?
- Who is authorized to change or update the AUP?
There are five key steps every organization must take to begin the process of preventing data loss: identify PII your organization must protect, prioritize PII, find where PII is located, create an AUP and educate your employees about your AUP. PII may be in multiple places, redundant on servers, laptops, PCs and removable media. Once found, an organization needs to define its AUPs for accessing and using the PII. AUPs will vary from organization to organization, but should accomplish three goals: protect PII data, define who can access PII and establish rules for how authorized employees can use PII.
The AUPs you develop will only be effective if your employees feel they have a part to play in protecting your PII. Comprehensively educating employees is a critical and often overlooked step. Deliver copies of AUPs to employees, offer training sessions and have them sign a statement acknowledging they will abide by the policies. This will make every employee an active participant in the enforcement of AUPs, and the organization-wide effort to prevent data loss and the loss of PII.
Five rating criteria to determine what data needs to be protected most are:
- distinguishability – look for data that by itself can identify a unique individual
- aggregation – look for two or more pieces of data that when combined can identify a unique individual
- how PII is stored, transmitted, used – frequently transmitted over networks, stored redundantly on servers or portable devices or used by many people in the organization
- compliance – an organization must comply with regulations and standards for protecting PII
- ease of access – decide if the PII is easily accessed by any employee, can be copied, sent and saved without restriction, is available for use by HR for employee management or by staff or Is not protected by PINs or passwords before being accessible by staff.
Solution choices
Strong, system-level security can prevent accidental data loss and stop malicious threats before they harm your organization, while ensuring the right employees have access to the data they need to do their jobs within established AUPs. There is no silver bullet to accomplish these goals. Rather, it requires a combination of technologies for defense-in-depth or a multilayer security strategy.
Encryption
Full-disk encryption:
- USB, CD and removable media encryption
- policy-based email encryption
- file share encryption
- central key management and backup
- ability to audit encryption status
Threat protection
Protect endpoint, email and web vectors with proven security:
- detect known and unknown malware proactively without the need for an update, including viruses, worms, Trojans, spyware, adware, suspicious files, suspicious behavior, potentially unwanted applications (PUAs) and more
- get antivirus, firewall, application and device control in a single agent
- defend all of your platforms (Windows, Mac, Linux, UNIX)
Data loss prevention
Stop accidental data loss by scanning content for sensitive information uploaded to websites, sent by email or IM, and saved on storage devices with automatic rules, such as:
- file matching rule: Specified action is taken based on name or type of file a user is attempting to access or transfer
- content rule: Contains one or more data definitions and specifies the action taken if a user attempts to transfer data that matches those definitions
Policy compliance
Develop a list of applications that need to be controlled under all or certain circumstances to prevent the accidental transmission of sensitive data, by email, IM, P2P, online storage, smartphone synchronization and other frequently used communications apps – introduce and enforce methods of web control, as the Internet is the source of most malware. Enable control of three types of devices that are commonly used in the accidental storage or sending of sensitive data:
- storage: removable storage devices ( these include USB flash drives, PC card readers, and external hard drives); optical media drives (CD-ROM/DVD/Blu-ray); floppy disk drives
- network: modems, wireless (Wi-Fi interfaces, 802.11 standard)
- short range: Bluetooth interfaces, infrared (IrDA infrared interfaces.
Protecting PII requires organizations to work through a number of steps. Exactly what an organization does under each step will vary depending on industry, the type of data held, the geographies worked in, attitude to risk, resources, and other factors.
