Sture Udd is CEO of UpCode and has 30 years as an entrepreneur in the information business, with UPC Center and UpCode of which he has been CEO since 1998. Sture Udd also serves on the advisory board of STFI Packforsk/Sweden and has been involved in the development of several patents and pending patents in mobile access and interaction (MAI tech). Over the years, he has worked with governments and enterprises in 60 countries in the field of mobile ID and mobile SmartCity.
An overview of the development of a wireless extension tool for handhelds used for inspecting e-tickets in passenger transport
 A cardless society is already mooted as a practical possibility. Mobile ID is a reality of this and, according to industry pundits, has a huge impact on the role of ID. A main issue raised for many countries is a potential and radical cost reduction in ID infrastructures and investment costs, as well as impact on the development of consumer services and services for civil society along with an highly increased efficiency in governmental enforcement and organization-related security. ID People spoke to Sture Udd, CEO of UpCode, to discuss security and other issues surrounding mobile ID, which he terms a quantum leap for societies.
A cardless society is already mooted as a practical possibility. Mobile ID is a reality of this and, according to industry pundits, has a huge impact on the role of ID. A main issue raised for many countries is a potential and radical cost reduction in ID infrastructures and investment costs, as well as impact on the development of consumer services and services for civil society along with an highly increased efficiency in governmental enforcement and organization-related security. ID People spoke to Sture Udd, CEO of UpCode, to discuss security and other issues surrounding mobile ID, which he terms a quantum leap for societies.
How is mobile technology changing the world as far as ID is concerned?
 The ID concept has been practically the same for two to three thousand years of civilization. There was always some kind of document or paper fro identifying someone, somewhere. But today, with mobile technology reaching new heights of functionality, accessibility and interconnectivity, I believe you do not need a document anymore and that means a total change, not in the technology but in the mentality of people. Consumers are already flooded with data – both personal and public with multiple IDs on different platforms for different usage – whether it is their national ID, driver’s license, online banking data or social profile on a media site. We need to ask what should people do with all this digital information, how it should be used and how can society gain? And this can only be achieve by a change in mindset.
The ID concept has been practically the same for two to three thousand years of civilization. There was always some kind of document or paper fro identifying someone, somewhere. But today, with mobile technology reaching new heights of functionality, accessibility and interconnectivity, I believe you do not need a document anymore and that means a total change, not in the technology but in the mentality of people. Consumers are already flooded with data – both personal and public with multiple IDs on different platforms for different usage – whether it is their national ID, driver’s license, online banking data or social profile on a media site. We need to ask what should people do with all this digital information, how it should be used and how can society gain? And this can only be achieve by a change in mindset.
In terms of changing perceptions, how big a challenge is it, especially when security is at stake – and the idea of having all our eggs in one basket?
In the mobile world, this is definitely a psychological attitude and it requires clarification. Many people believe their data and secure access codes and methodologies are all retained in the mobile phone. This is not the case as their data is not on the mobile – it is merely a connection device, so if you lose it , all you lose is the device as the data is held securely somewhere else. Conversely if you lose a traditional document such as an ID card or a passport, someone else can potential use it fraudulently.
How critical is the other challenge regarding authorities and enterprises whose agendas support the old concepts? In other words,, are there people who stand to lose business, market share and infrastructure investment if the new concept takes hold on a widespread basis?
 There are certainly legacy infrastructure issues in Europe, and we are in the midst of this challenge. We recently studied for example, a hospital where there were 120 different documents in circulation without any connectivity or interaction. They existed in silos. So this problem needs to be faced with new methods. There will be a need to build systems from bottom-up.
There are certainly legacy infrastructure issues in Europe, and we are in the midst of this challenge. We recently studied for example, a hospital where there were 120 different documents in circulation without any connectivity or interaction. They existed in silos. So this problem needs to be faced with new methods. There will be a need to build systems from bottom-up.
There is one case where it is being done top-down – and that is in India: this is exactly the right way to go forward, but not necessarily practical in countries where there are established infrastructures requiring major decisions to be taken surrounding all the security issues in order to initiate a big change. Top-down therefore is not the norm – we need to start with the technology, such as Google did – begin to use it and address the challenges as they emerge.
In Latin America and in Europe there are already examples where this bottomup solution is working. In the Middle East they have the political will and funding to initiate these projects and it is more than clear that the historical window is open for that region, where decisive moves can be made. They could can even do it better than in other countries and be a frontrunner.
In general, the introduction of mobile ID could for sure have a decisive impact on speed of development in developing countries and offer much needed help for restructuring governmental procedures in developed countries.
In personal security, if a mobile phone is used as an identity device, and it is lost, is there is a risk of having our ID stolen by someone else, is access to all data lost and can someone else gain access to it through the device?
 Here we should explain the safety and security of transactions and ID in the concept of cloud computing, which is where we in fact keep our data. It is not about the mobile phone. For example, you do not lose the driver’s license, if your device is lost or stolen, because it is not on the phone.
Here we should explain the safety and security of transactions and ID in the concept of cloud computing, which is where we in fact keep our data. It is not about the mobile phone. For example, you do not lose the driver’s license, if your device is lost or stolen, because it is not on the phone.
Intelligent scanning can solve this both in terms of ensuring security is upheld and inconvenience is addressed. This involves an intelligent digital procedure so no one else can use the phone and the rightful holder can access their data through another replacement device – or even temporarily, using a friend’s phone.
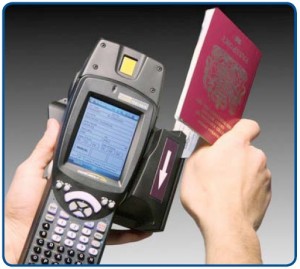
This would cover biometric data held centrally, as well as personal data for access to service. The security also will become even stronger as technology advances. For example, normally the idea of a passport is to enter a country if allowed by border control – whether technologically through an authentication system or personally with an immigration official.
This method is always potentially under threat of fake identities being used or fraud. In the new mobile world this is different, as the fraudster would need to fake everything, not just the ID or bank card. This means that when all secure data surrounding every transaction that needs to be made in someone’s daily life, the security is 10 times higher. Therefore fake IDs and counterfeits are no longer feasible in this scenario.
How would this translate into other areas and applications in terms of mobile ID being used for objects or information exchange on a commercial level?
 We are entering a new world of security in terms of thinking. Another interesting issue is food. For example, statistics show that 70 percent of Parma ham is faked. The same intelligent system of enabled mobile ID can be deployed to handle a situation such as this in the shop, so consumers can check if the product is fake at the counter using their mobile device, which has access to authenticating data. This is much more efficient in terms of time and money savings than a procedure that relies on security or enforcement officials checking what is fake and what is not. The consumer can do it – and would do it – as he has a vested interest in the product and its authenticity.
We are entering a new world of security in terms of thinking. Another interesting issue is food. For example, statistics show that 70 percent of Parma ham is faked. The same intelligent system of enabled mobile ID can be deployed to handle a situation such as this in the shop, so consumers can check if the product is fake at the counter using their mobile device, which has access to authenticating data. This is much more efficient in terms of time and money savings than a procedure that relies on security or enforcement officials checking what is fake and what is not. The consumer can do it – and would do it – as he has a vested interest in the product and its authenticity.
In addition, another example of the commercial space is in promotion. When the possibilities offered by the mobile phone are combined with printed media, the benefits are many. Print media obtain, among other things, measurability for their advertising, genuine interactivity and closer customer contacts. In this way current print product business models can be genuinely changed and their functionality expanded so that they are actually more efficient than electronic media.
This still utilizes the 2D bar code printed on paper – but more advanced. When a mobile phone’s camera is pointed at the code the phone activates various functions – for example, connects directly to a website.
This can be described as supermedia – when electronic media is linked in the right way to print media. We believe they should be developed together a print creates enthusiasm and awakens ideas, and it should be integrated into the opportunities created by e-media as one and the same package.
This also applies to be being is linked to print products and the others in mobile payments, education, healthcare and logistics, among other services. The next step is to integrate sensor technology with a 2D code. Sensor technology involves printing a spot with a sensor material which, for example, changes color in heat.
What do you foresee as the future in a mobile society?
Fundamentally, in all these cases – from personal ID to product promotion and communication, we are not talking about a new ‘document’, new packaging or a new technology here, we are talking about a new level for a really smart society.
One where we are not saddled with costs and inefficiencies generated by security issues, but rather, where everything is more efficient and encourages higher levels of trust.
